Set up SCIM EnterpriseEnterprise +
The System for Cross-Domain Identity Management (SCIM) makes user data more secure and simplifies the admin and end-user lifecycle experience by automating user identities and groups. You can create or disable user identities in your Identity Provider (IdP), and SCIM will automatically make those changes in near real-time downstream in dbt.
Prerequisites
To configure SCIM in your dbt environment:
- You must be on an Enterprise or Enterprise+ plan.
- You must use Okta or Entra ID as your SSO provider and have it connected in the dbt platform.
- You must have permissions to configure the account settings in dbt platform and change application settings in Okta.
- If you have IP restrictions enabled, you must add Okta's IPs to your allowlist. If you're using Entra ID with IP restrictions enabled, refer to Azure SCIM provisioning fails due to IP allowlisting in the SCIM FAQ.
Supported features
The currently available supported features for SCIM are:
- User provisioning and de-provisioning
- User profile updates
- Group creation and management
- Importing groups and users
When SCIM is enabled, the following functionality will change:
- Users are not automatically added to default groups
- Manual actions such as inviting users, updating user information and updating group memberships are disabled by default
- SSO group mappings are disabled in favor of SCIM group management. Refer to Do SSO group mappings still apply when SCIM is enabled? for details.
To overwrite these updates to functionality with SCIM enabled, enable manual updates as part of the SCIM configuration (not recommended).
When users are provisioned, the following attributes are supported
- Username
- Family name
- Given name
The following IdPs are supported in the dbt user interface:
If your IdP isn't on the list, it can be supported using dbt APIs.
Set up dbt
To retrieve the necessary dbt configurations for use in Okta or Entra ID:
- Navigate to your dbt Account settings.
- Under Settings, click SSO & SCIM.
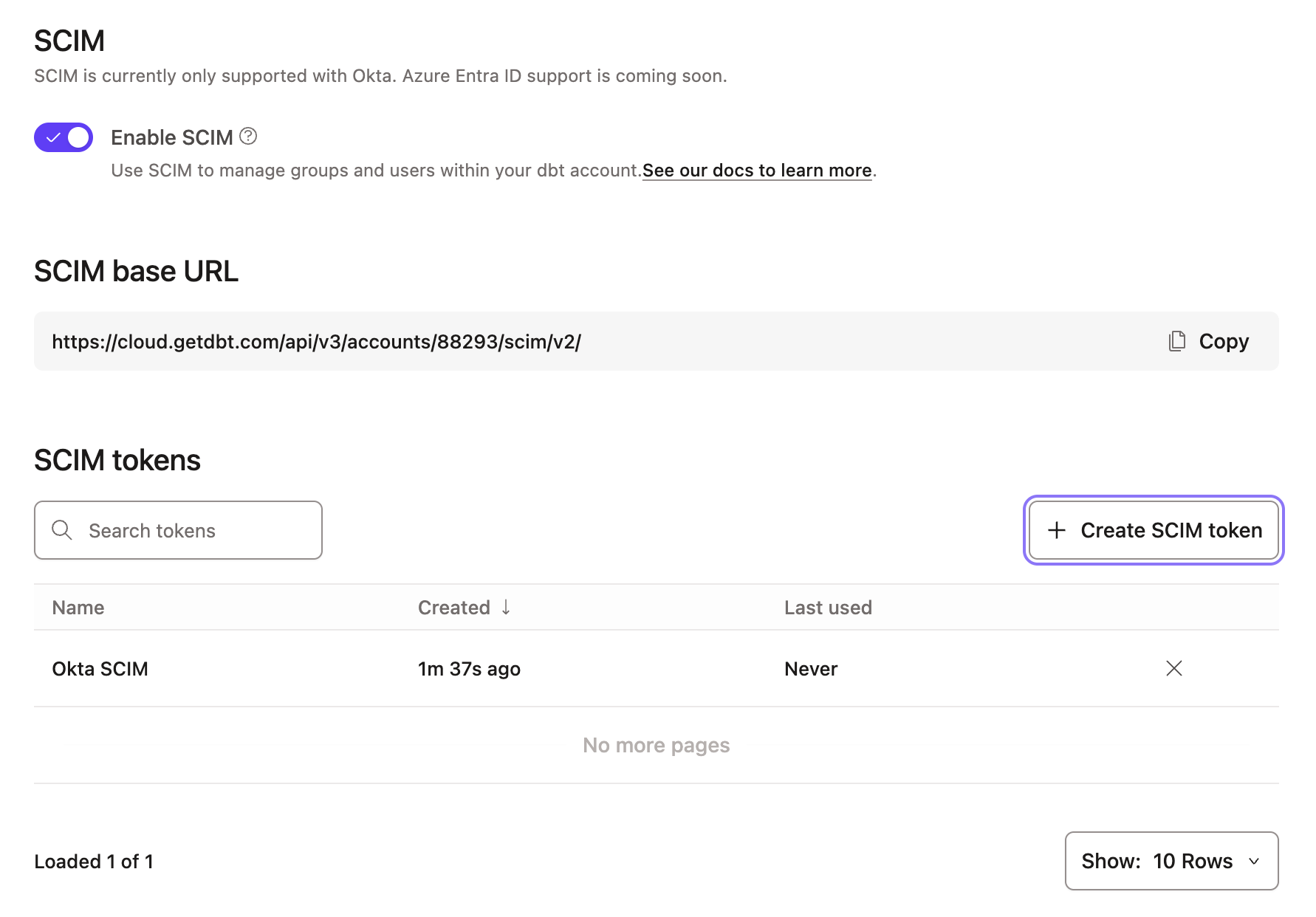
- Scroll to the bottom of your SSO configuration settings and click Enable SCIM.
- Record the SCIM base URL field for use in a later step.
- Click Create SCIM token.
note
To follow best practices, you should regularly rotate your SCIM tokens. To do so, follow these same instructions you did to create a new one. To avoid service disruptions, remember to replace your token in your IdP before deleting the old token in dbt.
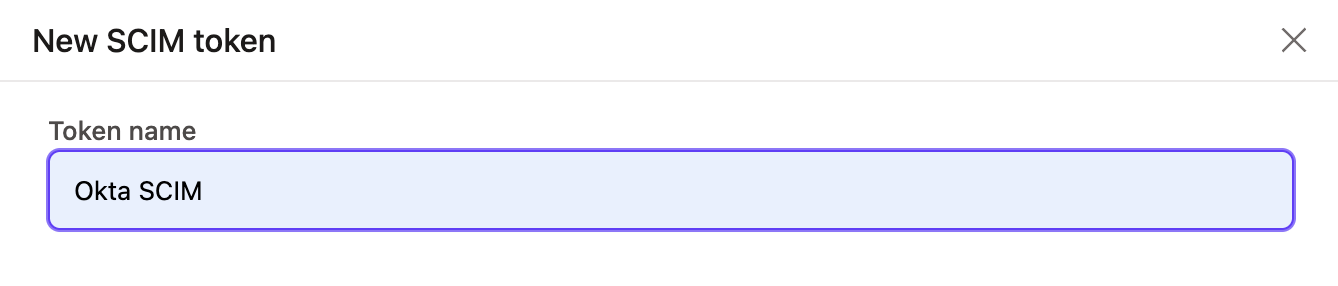
- In the pop-up window, give the token a name that will make it easily identifiable. Click Save.
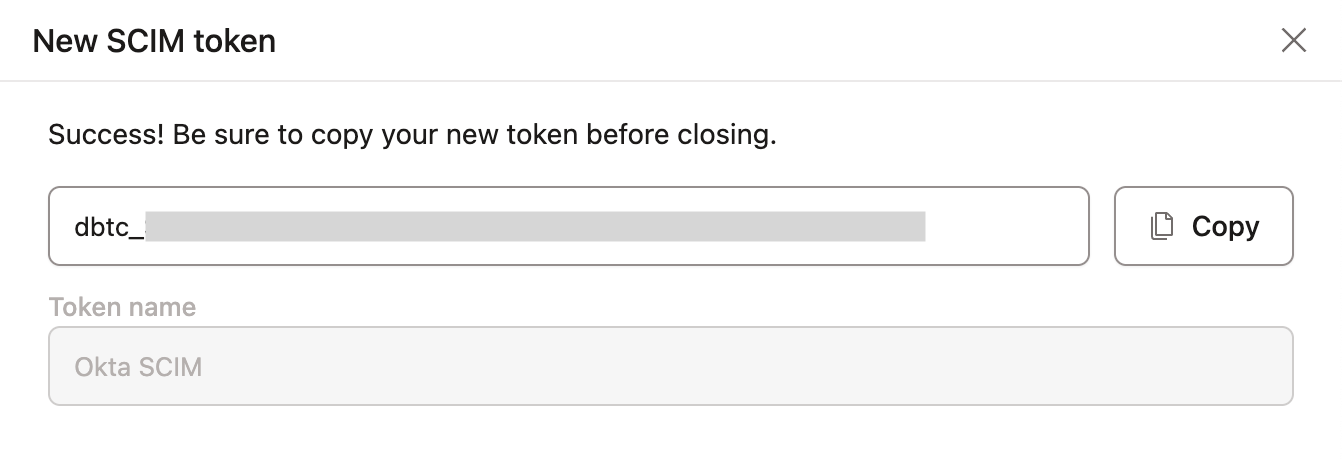
- Copy the token and record it securely, as it will not be available again after you close the window. You must create a new token if you lose the current one.
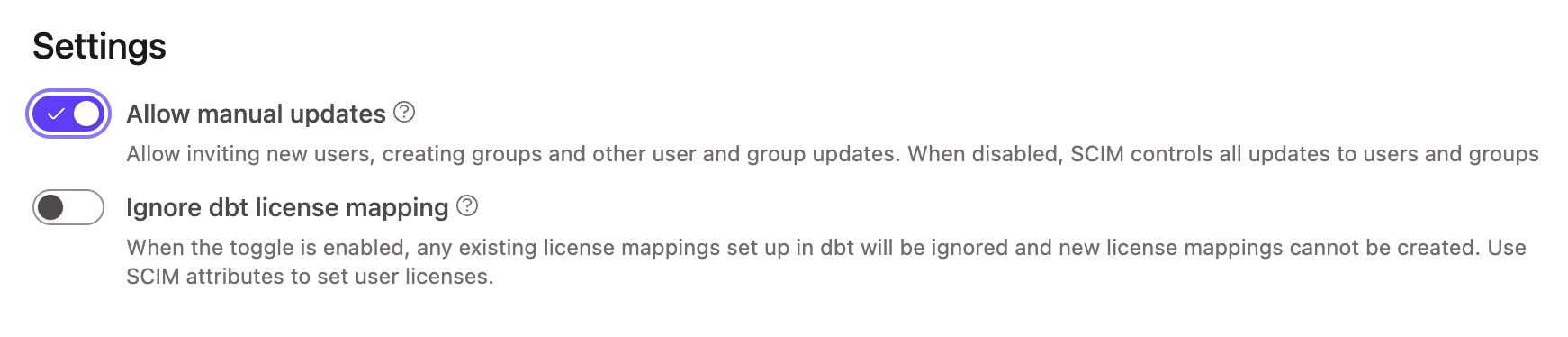
- (Optional) Manual updates are turned off by default for all SCIM-managed entities, including the ability to invite new users manually. This ensures SCIM-managed entities stay in sync with the IdP, and we recommend keeping this setting disabled.
- However, if you need to make manual updates (like update group membership for a SCIM-managed group), you can enable this setting by clicking Allow manual updates and confirming the Allow manual updates pop up. For more details on this setting, refer to What does "Allow manual updates" mean? in the SCIM FAQ.
Next steps
Configure SCIM for your identity provider and optionally manage licenses:
- Set up SCIM with Okta — User and group provisioning, profile updates, and license management (Okta only).
- Set up SCIM with Entra ID — User and group provisioning and profile updates, plus assigning users to the SCIM app.
- SCIM FAQs and troubleshooting — Common questions and troubleshooting for SCIM provisioning.
Was this page helpful?
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.