Set up SSO with Google Workspace EnterpriseEnterprise +
dbt Enterprise-tier plans support Single-Sign On (SSO) via Google GSuite. You will need permissions to create and manage a new Google OAuth2 application, as well as access to enable the Google Admin SDK. Gsuite is a component within Google Cloud Platform (GCP), so you will also need access to a login with permissions to manage the GSuite application within a GCP account.
Some customers choose to use different cloud providers for User and Group permission setup than for hosting infrastructure. For example, it's certainly possible to use GSuite to manage login information and Multifactor Authentication (MFA) configuration while hosting data workloads on AWS.
Currently supported features include:
- SP-initiated SSO
- Just-in-time provisioning
This guide outlines the setup process for authenticating to dbt with Google GSuite.
Configuration of the GSuite organization within GCP
dbt uses a Client ID and Client Secret to authenticate users of a GSuite organization. The steps below outline how to create a Client ID and Client Secret for use in dbt.
Creating credentials
- Navigate to the GCP API Manager
- Select an existing project, or create a new project for your API Credentials
- Click on Create Credentials and select OAuth Client ID in the resulting popup
- Google requires that you configure an OAuth consent screen for OAuth credentials. Click the Configure consent screen button to create a new consent screen if prompted.
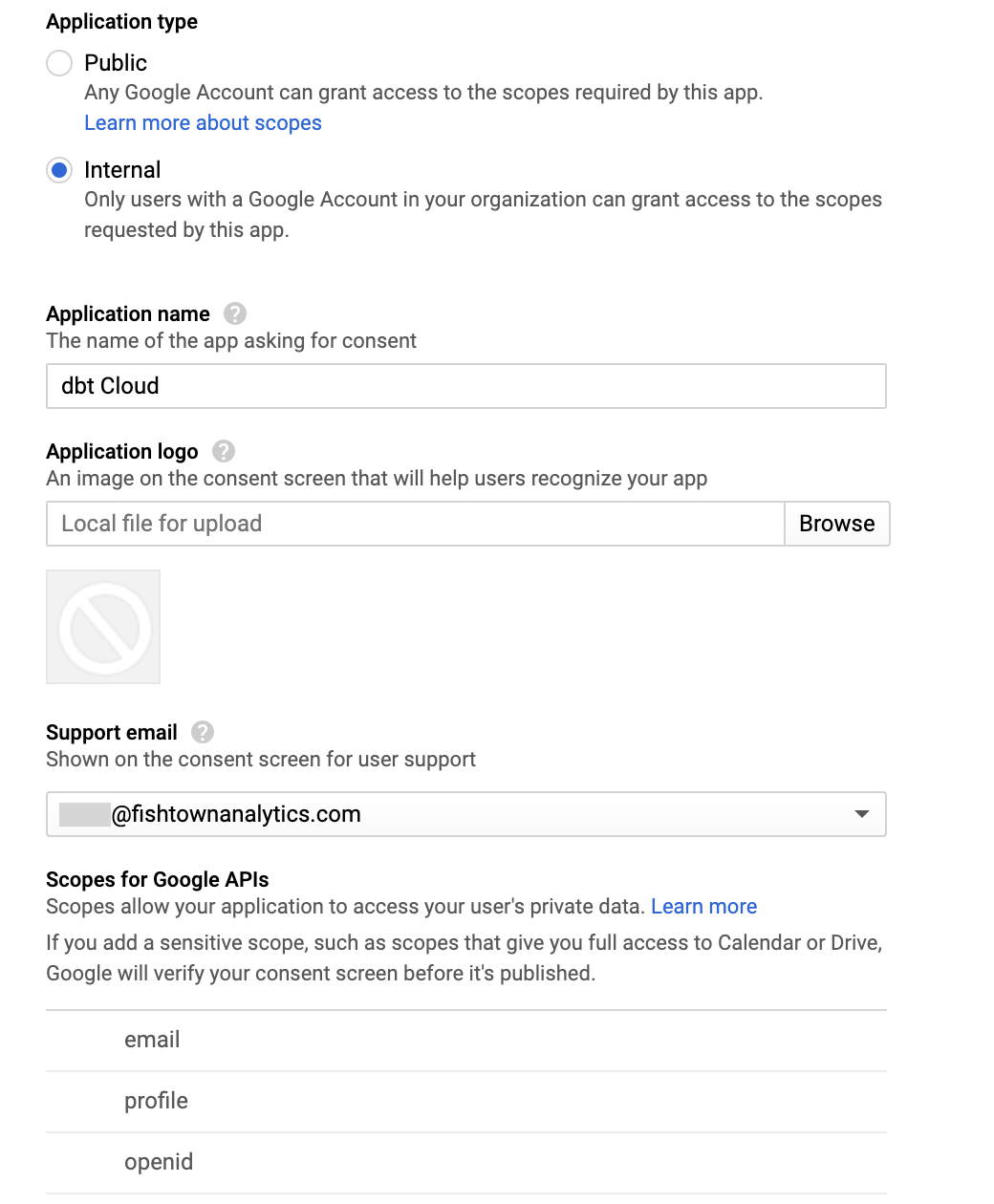
- On the OAuth consent screen page, configure the following settings (Google docs):
| Loading table... |
- Save the Consent screen settings to navigate back to the Create OAuth client id page.
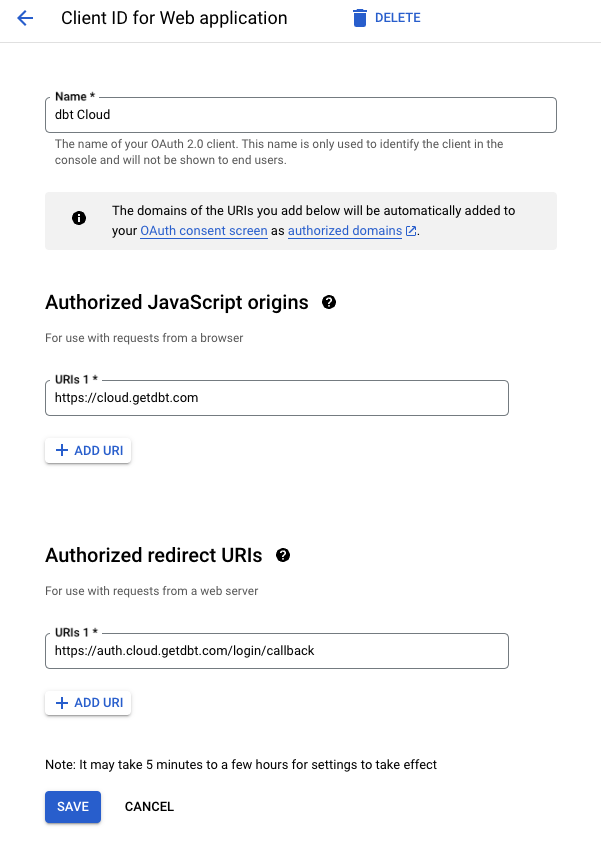
- Use the following configuration values when creating your Credentials, replacing
YOUR_ACCESS_URLandYOUR_AUTH0_URI, which need to be replaced with the appropriate Access URL and Auth0 URI from your account settings.
| Loading table... |
- Press "Create" to create your new credentials. A popup will appear with a Client ID and Client Secret. Write these down as you will need them later!
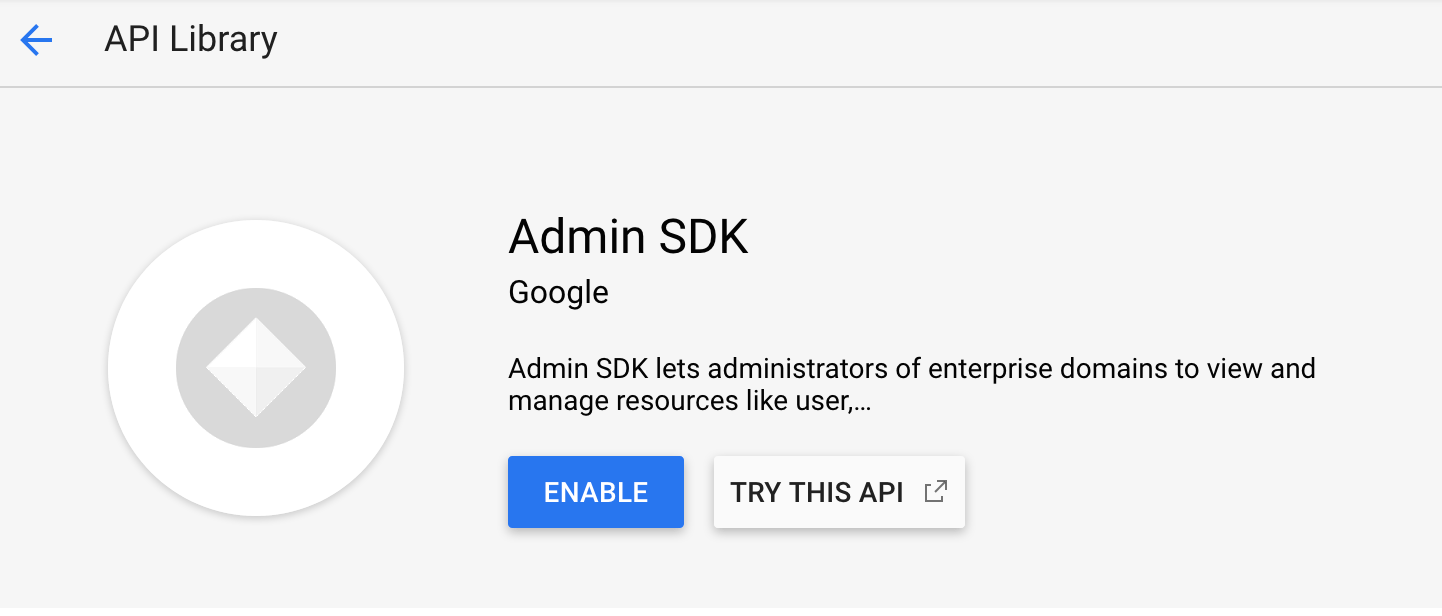
Enabling the Admin SDK
dbt requires that the Admin SDK is enabled in this application to request Group Membership information from the GSuite API. To enable the Admin SDK for this project, navigate to the Admin SDK Settings page and ensure that the API is enabled.
Configuration in dbt
To complete setup, follow the steps below in the dbt application.
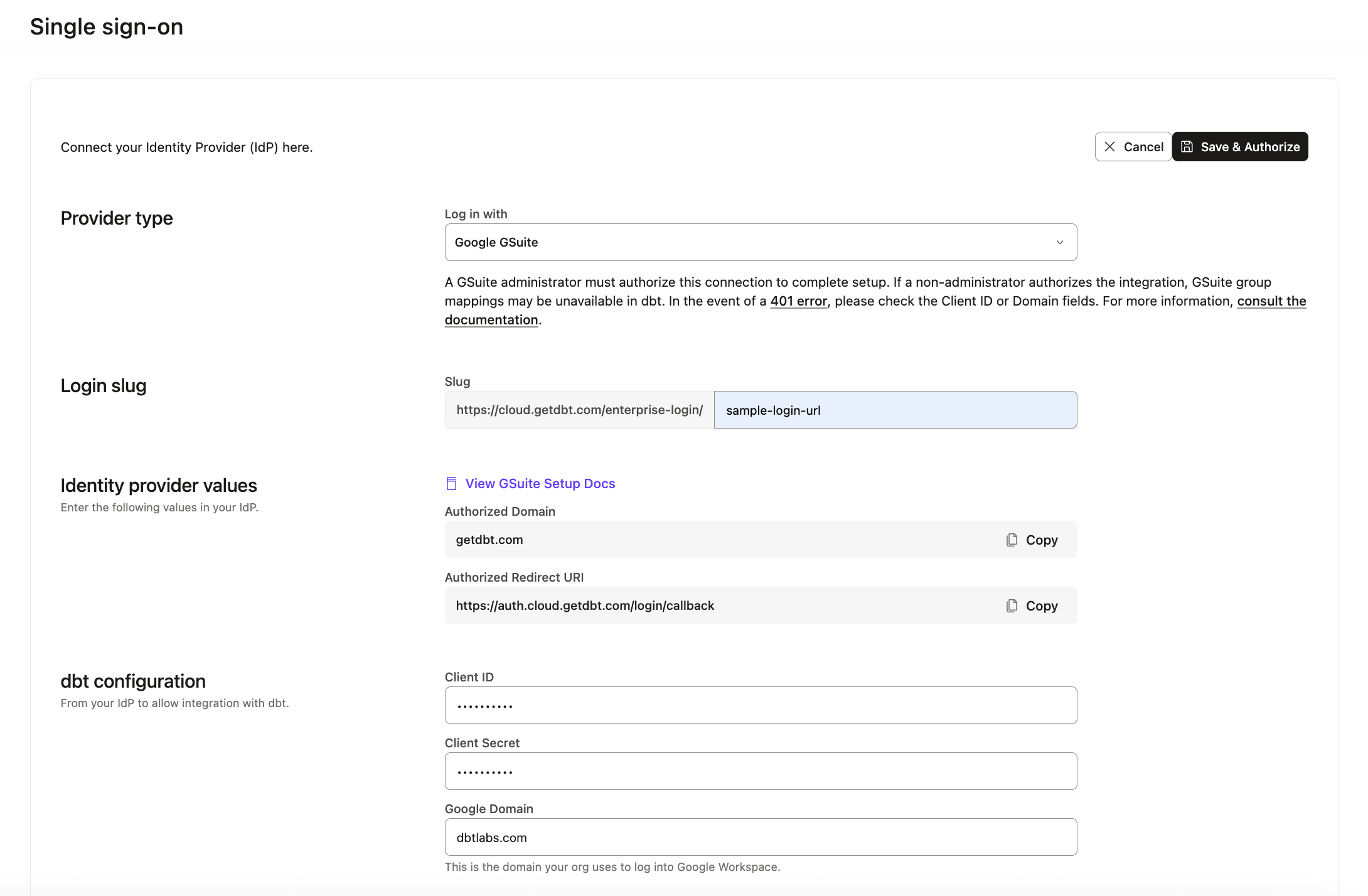
Supply your OAuth Client ID and Client Secret
-
Navigate to the Enterprise > Single Sign On page under Account settings.
-
Click the Edit button and supply the following SSO details:
- Log in with: GSuite
- Client ID: Paste the Client ID generated in the steps above
- Client Secret: Paste the Client Secret generated in the steps above
- Domain in GSuite: Enter the domain name for your GSuite account (eg.
dbtlabs.com). Only users with an email address from this domain will be able to log into your dbt account using GSuite auth. Optionally, you may specify a CSV of domains which are all authorized to access your dbt account (eg.dbtlabs.com, fishtowndata.com)
-
Click Save & Authorize to authorize your credentials. You should be dropped into the GSuite OAuth flow and prompted to log into dbt with your work email address. If authentication is successful, you will be redirected back to the dbt application.
-
On the Credentials page, verify that a
groupsentry is present, and that it reflects the groups you are a member of in GSuite. If you do not see agroupsentry in the IdP attribute list, consult the following Troubleshooting steps.
If the verification information looks appropriate, then you have completed the configuration of GSuite SSO.
Users can now log into dbt platform by navigating to the following URL, replacing LOGIN-SLUG with the value used in the previous steps and YOUR_ACCESS_URL with the appropriate Access URL for your region and plan:
https://YOUR_ACCESS_URL/enterprise-login/LOGIN-SLUG
Setting up RBAC
Now you have completed setting up SSO with GSuite, the next steps will be to set up RBAC groups to complete your access control configuration.
Troubleshooting
Invalid client error
If you experience an Error 401: invalid_client when authorizing with GSuite, double check that:
- The Client ID provided matches the value generated in the GCP API Credentials page.
- Ensure the Domain Name(s) provided matches the one(s) for your GSuite account.
OAuth errors
If OAuth verification does not complete successfully, double check that:
- The Admin SDK is enabled in your GCP project
- The Client ID and Client Secret provided match the values generated in the GCP Credentials page
- An Authorized Domain was provided in the OAuth Consent Screen configuration
If authentication with the GSuite API succeeds but you do not see a
groupsentry on the Credentials page, then you may not have permissions to access Groups in your GSuite account. Either request that your GSuite user is granted the ability to request groups from an administrator, or have an administrator log into dbt and authorize the GSuite integration.
Learn more
Was this page helpful?
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.