Configuring Snowflake PrivateLink Enterprise +
This feature is available on the following dbt Enterprise tiers:
- Enterprise+
- Virtual Private
To learn more about these tiers, contact us at sales@getdbt.com.
The following steps walk you through the setup of an AWS-hosted Snowflake PrivateLink endpoint in a dbt multi-tenant environment.
Private connection endpoints can't connect across cloud providers (AWS, Azure, and GCP). For a private connection to work, both dbt and the server (like Snowflake) must be hosted on the same cloud provider. For example, dbt hosted on AWS cannot connect to services hosted on Azure, and dbt hosted on Azure can’t connect to services hosted on GCP.
Users connecting to Snowflake using Snowflake OAuth over an AWS PrivateLink connection from dbt will also require access to a PrivateLink endpoint from their local workstation. Where possible, use Snowflake External OAuth instead to bypass this limitation.
From the Snowflake docs:
Currently, for any given Snowflake account, SSO works with only one account URL at a time: either the public account URL or the URL associated with the private connectivity service
Configure AWS PrivateLink
This section walks you through the setup of an AWS-hosted Snowflake PrivateLink endpoint in a dbt platform. You can set up in two ways:
- Self-serve private endpoints: Self-serve configuration of Snowflake PrivateLink endpoints directly in dbt platform user interface. Currently in private beta.
- Support-led setup: Requires contacting dbt Support to configure Snowflake PrivateLink endpoints. Non-self service configuration of Snowflake PrivateLink endpoints.
Self-serve private endpoints Private beta
Self-serve private endpoints are currently in private beta for Snowflake on AWS. To join the beta, please reach out to your account manager.
This feature isn't available for Azure or GCP. If you don't see Private endpoints in your account settings, use the Support-led setup instead.
This section walks you through the process of requesting a new Snowflake PrivateLink endpoint in dbt platform.
Prerequisites
- Account admin or Project creator permission sets in dbt platform. Users with an IT license can also create private endpoints.
- Snowflake
ACCOUNTADMINpermissions.
Before you begin
Before requesting a private endpoint, allowlist dbt Labs' AWS account in Snowflake. This is a one-time setup per Snowflake account and is handled through a Snowflake support case, which can take time — complete it before starting the request flow.
-
Open a support case with Snowflake to allow access from the dbt AWS account.
- Snowflake prefers that the account owner opens the support case directly rather than dbt Labs acting on their behalf. For more information, refer to Snowflake's knowledge base article.
- Provide your dbt account ID along with any other information requested in the article.
- AWS account ID:
346425330055— Note: This account ID only applies to AWS dbt multi-tenant environments. For AWS Virtual Private/Single-Tenant account IDs, contact dbt Support.
- AWS account ID:
-
Wait for Snowflake to confirm access has been granted before proceeding.
Request a new private endpoint
After Snowflake confirms they've allowlisted dbt Labs' AWS account in Snowflake, you can request a new private endpoint. Follow these steps to do so:
-
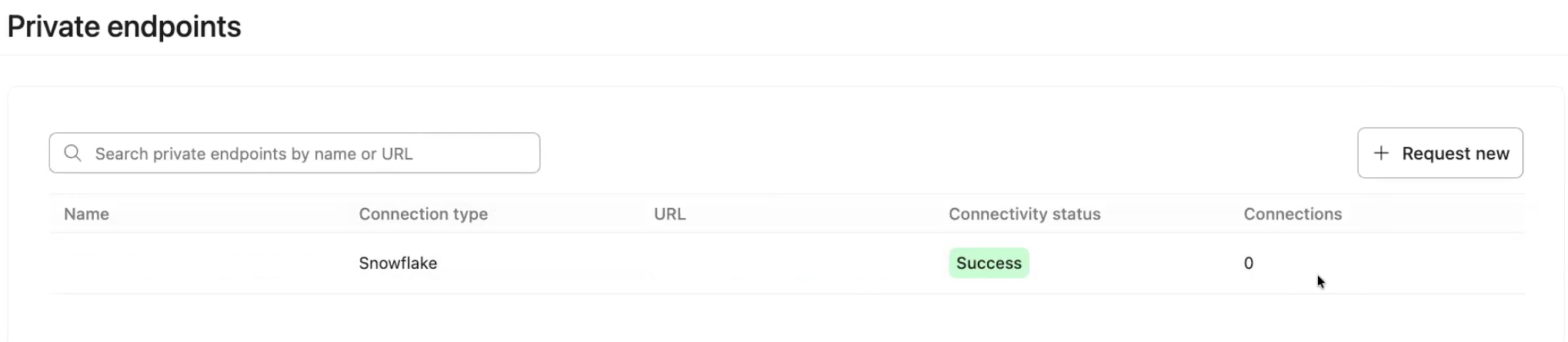
In dbt platform, go to Account settings → Integrations → Private endpoints.
-
In the Private endpoints table, review your existing endpoints. The table shows all private endpoints in your account (including non-Snowflake ones) with the following details:
- Name
- Connection type (for example, Snowflake)
- URL
- Connectivity status (for example, Success or Unknown)
- Connections — the number of dbt platform connections using the endpoint
You can search by Name or URL. You can only create new endpoints for Snowflake at this time. To delete an endpoint, contact dbt Support.
-
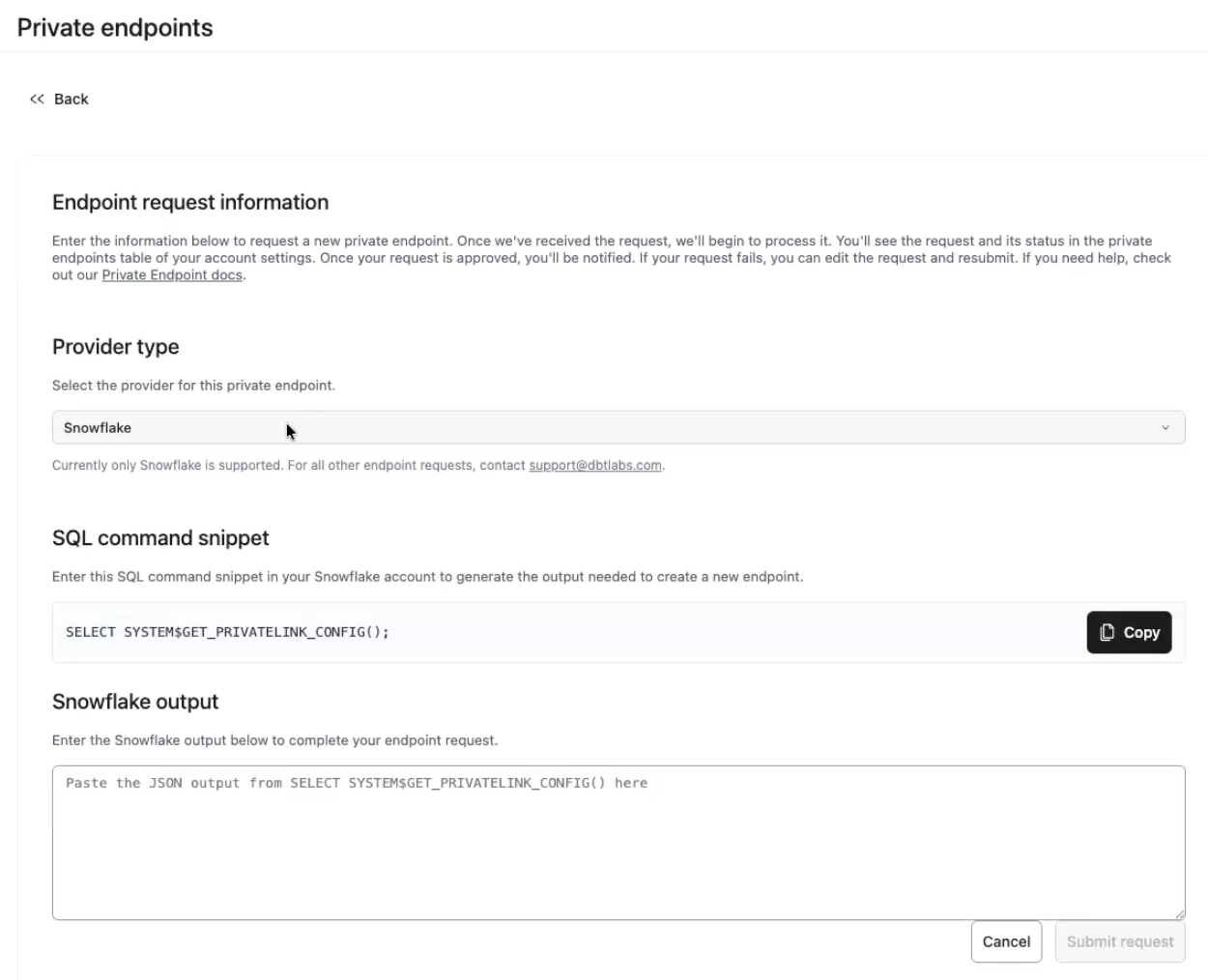
To request a new endpoint, click Request new.
-
Under Provider type, confirm Snowflake is selected. Currently other endpoint providers aren't supported, contact dbt Support if you need to connect to a different service.
-
Copy the SQL command in the SQL command snippet section.
-
Go to Snowflake and run the SQL command snippet you copied from dbt platform:
SELECT SYSTEM$GET_PRIVATELINK_CONFIG(); -
Copy the output from Snowflake and return to dbt platform to paste it into the Snowflake output field. If the output is correct, you'll see an inline Output looks good type message below the text box. If there's an error, review the message and make any updates as necessary.
-
Click Submit request.
-
After submission, a confirmation popup appears (for example, Endpoint request submitted). From the popup, you can request another endpoint or return to Private endpoints to track request status.
-
Proceed to the Connections page and following the steps in the Create connection in dbt section to configure PrivateLink. Once you configure PrivateLink on the Connections page, you'll see the new endpoint appear under Private endpoints → Associated connections.
If the connection test fails immediately after setup, this is expected — it doesn't mean something is wrong. DNS changes can take a few minutes to propagate. Wait a few minutes, then test again before contacting support.
Duplicate endpoint requests
If you submit a request using a VPCE ID that matches an existing endpoint, dbt platform displays an Endpoint already exists popup with two options:
- Reuse existing interface endpoint (default, recommended) — Links the new private endpoint to an already-approved interface endpoint. Use this option when your VPCE is already approved to avoid duplicating infrastructure.
- Create new interface endpoint — Creates a new interface endpoint with its own network policy. Use this only if you need a distinct network policy configuration.
Select your preferred option and click Confirm & Submit.
 Endpoint already exists popup with options to create a new interface endpoint or re-use an existing one
Endpoint already exists popup with options to create a new interface endpoint or re-use an existing oneTroubleshooting and errors
If an endpoint request fails, dbt platform displays error details that are safe to share externally.
If you see a failure state without clear next steps, collect the request details (endpoint name, creation time, status, and the Snowflake output you provided) and contact dbt Support.
Support-led setup
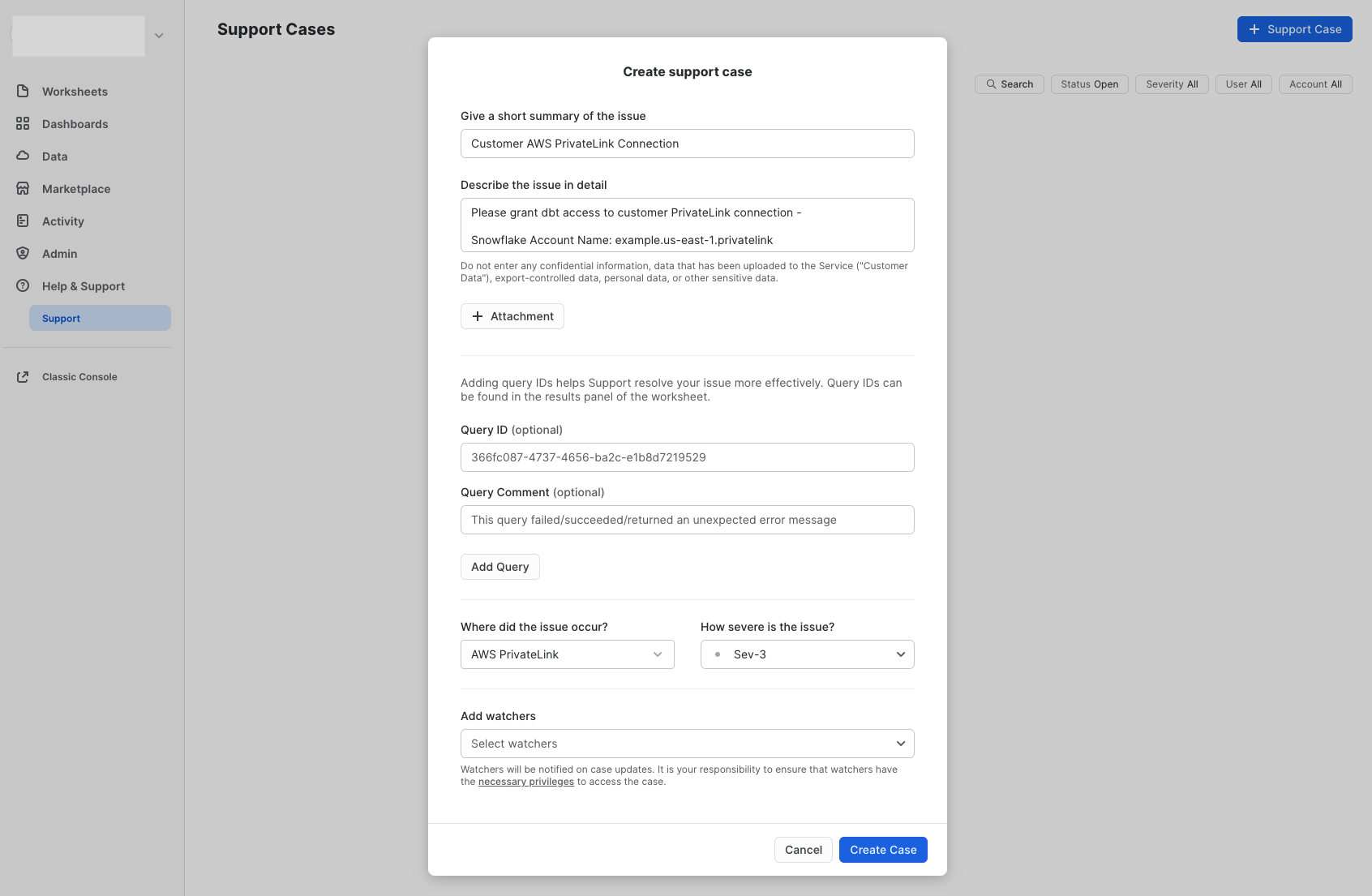
If Private endpoints is not available in your account settings, configure Snowflake PrivateLink by following these steps and submitting a request to dbt Support.
To configure Snowflake instances hosted on AWS for PrivateLink:
- Open a support case with Snowflake to allow access from the dbt AWS account.
- Snowflake prefers that the account owner opens the support case directly rather than dbt Labs acting on their behalf. For more information, refer to Snowflake's knowledge base article.
- Provide them with your dbt account ID along with any other information requested in the article.
- AWS account ID:
346425330055— Note: This account ID only applies to AWS dbt multi-tenant environments. For AWS Virtual Private/Single-Tenant account IDs, contact dbt Support.
- AWS account ID:
- You need Snowflake's
ACCOUNTADMINpermissions.
-
After Snowflake has granted the requested access, run the Snowflake system function SYSTEM$GET_PRIVATELINK_CONFIG and copy the output.
-
Add the required information to the following template and submit your request to dbt Support:
*By default, dbt will be configured to use privatelink-account-url from the provided SYSTEM$GET_PRIVATELINK_CONFIG as the PrivateLink endpoint. Upon request, regionless-privatelink-account-url can be used instead.
** Internal Stage PrivateLink must be enabled on the Snowflake account to use this feature
dbt Labs will work on your behalf to complete the private connection setup. Please allow 3-5 business days for this process to complete. Support will contact you when the endpoint is available.
Create connection in dbt
Once dbt Support completes the configuration, you can start creating new connections using PrivateLink.
- Navigate to Settings → Create new project → select Snowflake.
- You will see two radio buttons: Public and Private. Select Private.
- Select the private endpoint from the dropdown (this automatically populates the hostname/account field).
- Configure the remaining data platform details.
- Test your connection and save it.
Configuring internal stage PrivateLink in dbt
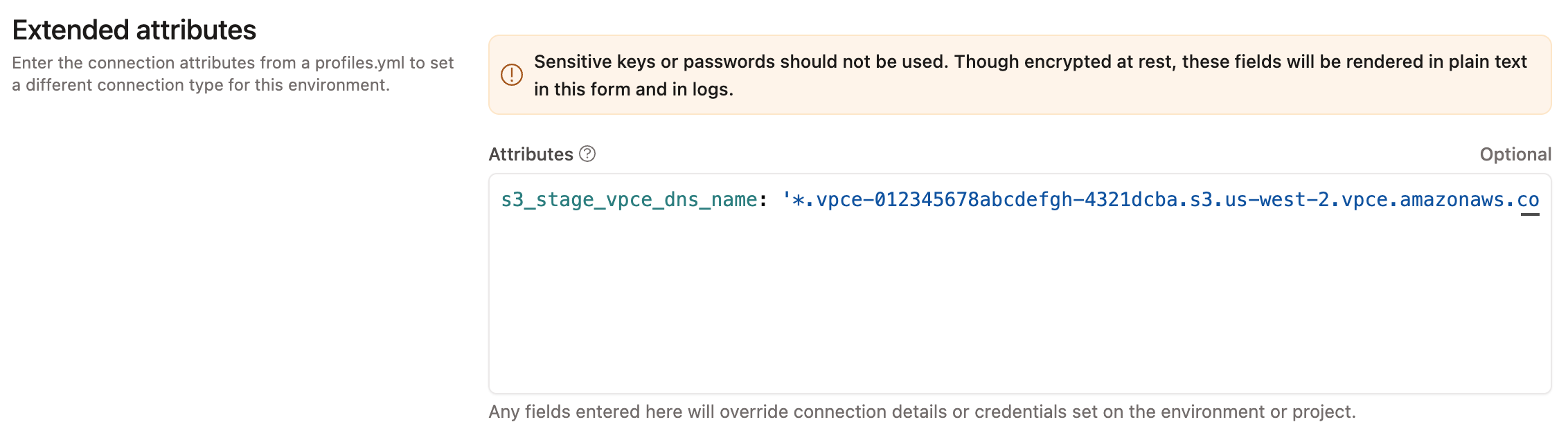
If an Internal Stage PrivateLink endpoint has been provisioned, your dbt environments must be configured to use this endpoint instead of the account default set in Snowflake.
- Obtain the Internal Stage PrivateLink endpoint DNS from dbt Support. For example,
*.vpce-012345678abcdefgh-4321dcba.s3.us-west-2.vpce.amazonaws.com. - In the appropriate dbt project, navigate to Orchestration → Environments.
- In any environment that should use the dbt Internal Stage PrivateLink endpoint, set an Extended Attribute similar to the following:
s3_stage_vpce_dns_name: '*.vpce-012345678abcdefgh-4321dcba.s3.us-west-2.vpce.amazonaws.com'
- Save the changes.
Configuring network policies
If your organization uses Snowflake Network Policies to restrict access to your Snowflake account, you need to add a network rule for dbt.
You can request the VPCE IDs from dbt Support, that you can use to create a network policy. If creating an endpoint for Internal Stage, the VPCE ID will be different from the VPCE ID of the main service endpoint.
For guidance on protecting both the Snowflake service and Internal Stage consult the Snowflake network policies and network rules docs.
Using the UI
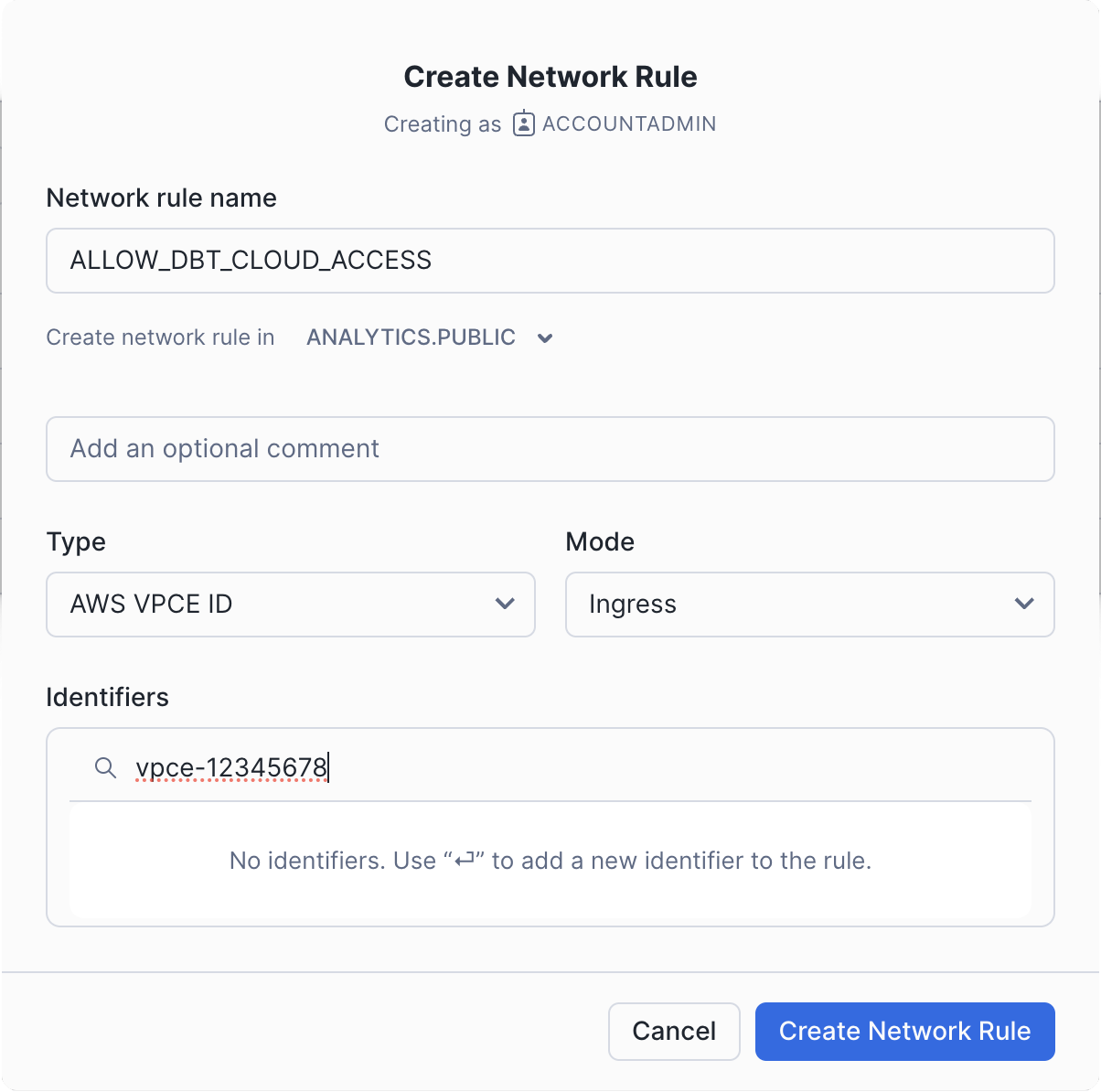
Open the Snowflake UI and take the following steps:
- Go to the Security tab.
- Click on Network Rules.
- Click on Add Rule.
- Give the rule a name.
- Select a database and schema where the rule will be stored. These selections are for permission settings and organizational purposes; they do not affect the rule itself.
- Set the type to
AWS VPCE IDand the mode toIngress. - Type the VPCE ID provided by dbt Support into the identifier box and press Enter.
- Click Create Network Rule.
-
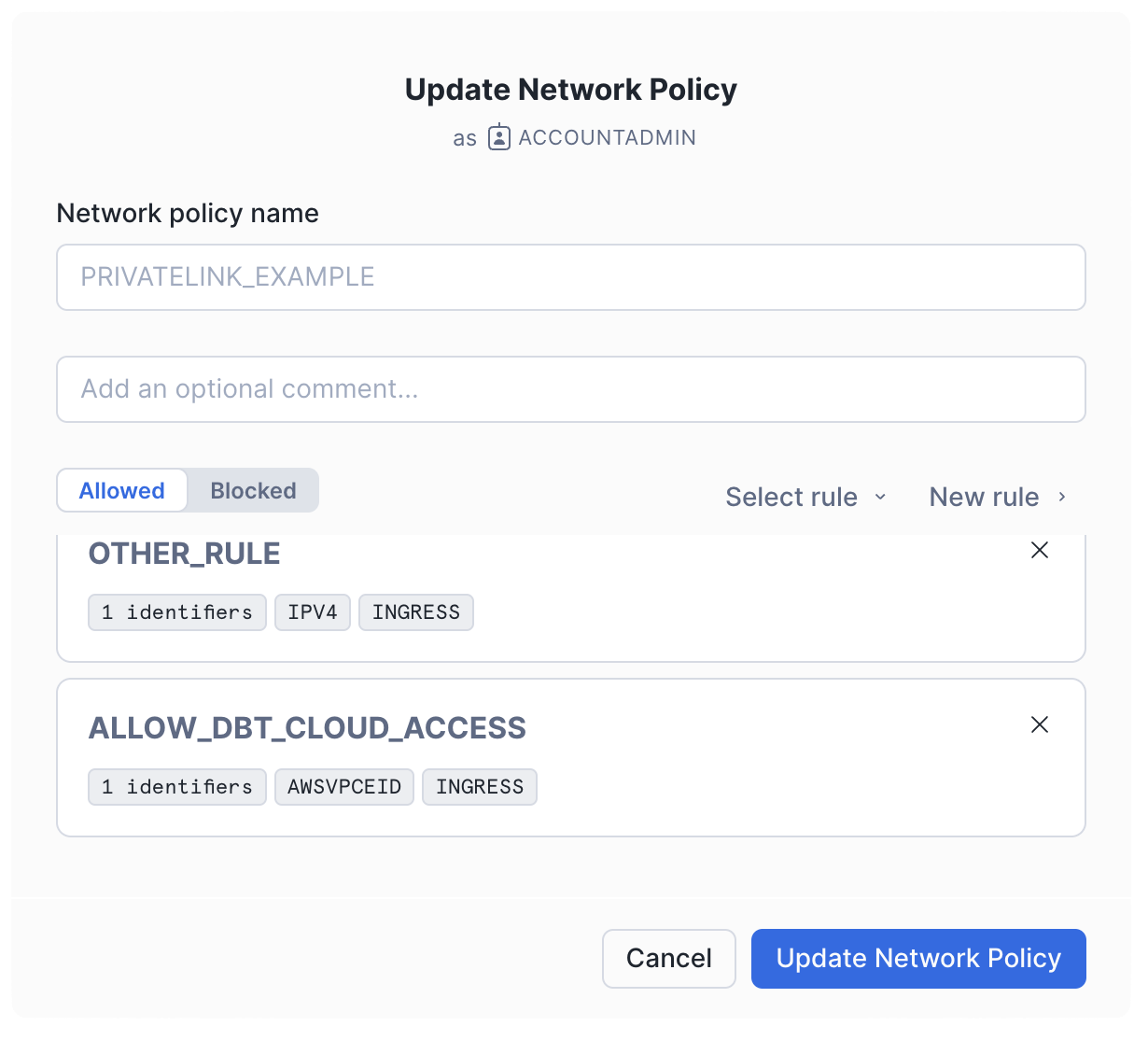
In the Network Policy tab, edit the policy you want to add the rule to. This could be your account-level policy or a policy specific to the users connecting from dbt.
-
Add the new rule to the allowed list and click Update Network Policy.
Using SQL
For quick and automated setup of network rules via SQL in Snowflake, the following commands allow you to create and configure access rules for dbt. These SQL examples demonstrate how to add a network rule and update your network policy accordingly.
- Create a new network rule with the following SQL:
CREATE NETWORK RULE allow_dbt_cloud_access
MODE = INGRESS
TYPE = AWSVPCEID
VALUE_LIST = ('<VPCE_ID>'); -- Replace '<VPCE_ID>' with the actual ID provided
- Add the rule to a network policy with the following SQL:
ALTER NETWORK POLICY <network_policy_name>
ADD ALLOWED_NETWORK_RULE_LIST =('allow_dbt_cloud_access');
Was this page helpful?
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.